US and Russia Account For 54% of Global Spam
Share
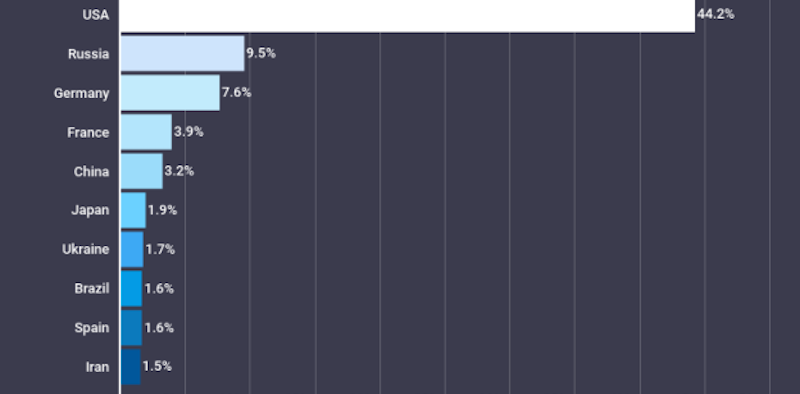
According to the data analyzed by the Atlas VPN team, 54% of spam emails in the last six months originated from two global superpowers — the United States and Russia.
While spammers in the US were behind a whopping 44% of global spam emails, Russiafollowed in second, accounting for nearly 10%.
Germany occupies the third spot in the list. Close to 8% of the spam emails sent in the last six months originated in the country. In the meantime, France sent out 4% of global spam emails.
China, another global superpower, rounds out the top five list of countries that distributed most spam emails over the past six months. Despite the country reinforcing internet censorship, a little over 3% of spam emails originated in China.
“Nearly a third of spam emails are dangerous.”
Spam mail is notorious for being annoying. However, few know that such emails may be dangerous and contain links that lead to phishing sites or malicious attachments that can install malware on your device.
In the past two weeks, 24,265 spam emails were sent worldwide. Overall, 8,076 or 33% of such emails were malicious.
The majority, 5,699 spam emails, were phishing attacks. They made up more than 23% of all such emails distributed in this period of time. In the meantime, 1,783 or 7% of spam emails were blackmail, while 594 or 2% were scam emails.
Rachel Welch, COO of Atlas VPN, gives advice on how to protect against email spam attacks:
“I recommend creating a complex email address, so spammers are less likely to guess it. What is more, avoid using your main email address to sign up for services online.
Rather, create multiple alias addresses linked to your core email address and use them when registering for services. This way, if you receive spam mail to one of your emails, you will be able to track it back to a specific website and block it.
Most importantly, if you do receive a suspicious email, never click on any link or attachment provided there. Such emails may contain malware that can infect your device and compromise your data.”
To read the full article, head over to:
https://atlasvpn.com/blog/us-and-russia-account-for-54-of-global-spam-volume-within-last-180-days